The Listener
The Listener is a data aesthetics installation exploring how we can create new forms of sense-making for the discrete, personal forms of data created and broadcast by our smartphones, laptops, and tablets.
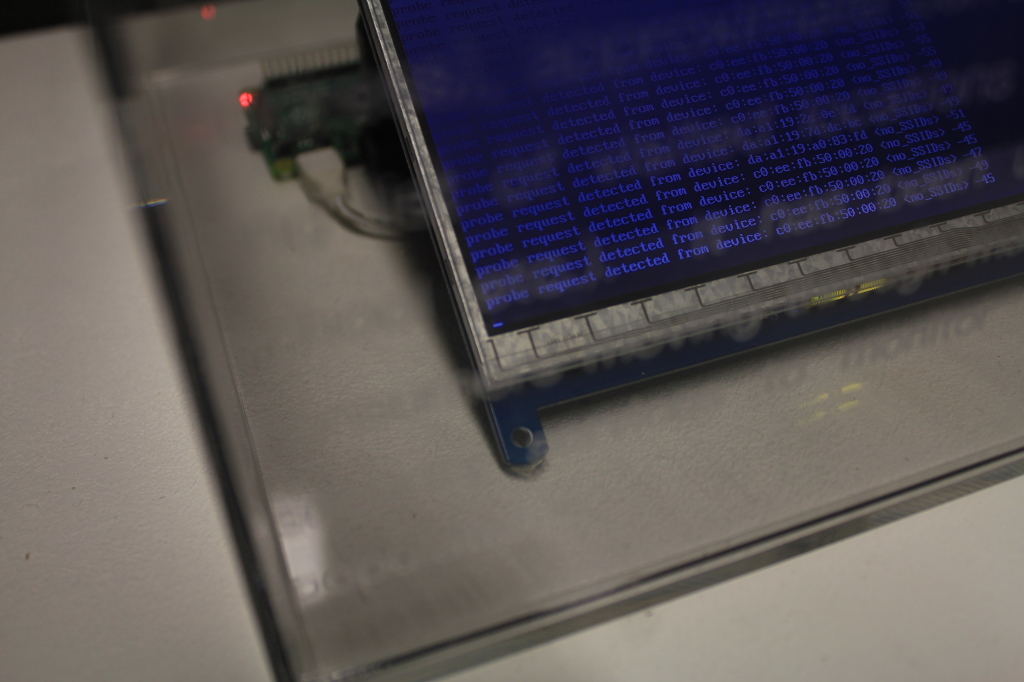
The Listener focuses on the ‘probe request’ – an initial stage of the wireless networking protocol IEEE 802.11, a standard that underpins the WiFi networks we encounter every day. The probe request is sent from wireless devices to any nearby networks, containing data such as the device’s MAC address (a unique hardware idenitifer), signal strength (roughly correlable to distance from the network) and often a list of SSIDs (service set identifiers, commonly called wireless network names) that the device has previously connected to (such as the wireless networks at your home, work, school, local coffee shop, airports you’ve visited, etc.). Probe requests are typically sent when a phone is unlocked or searching for networks, and most devices can send probe requests up to ten times per second to any wireless network in range.
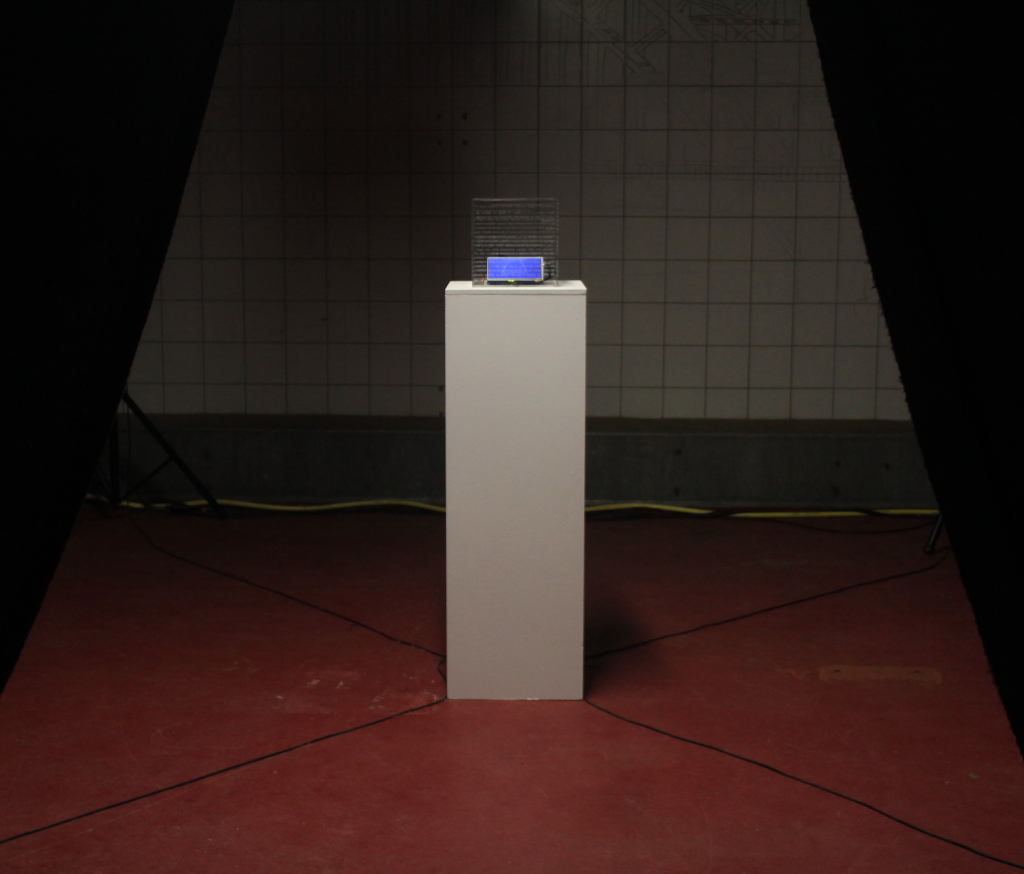
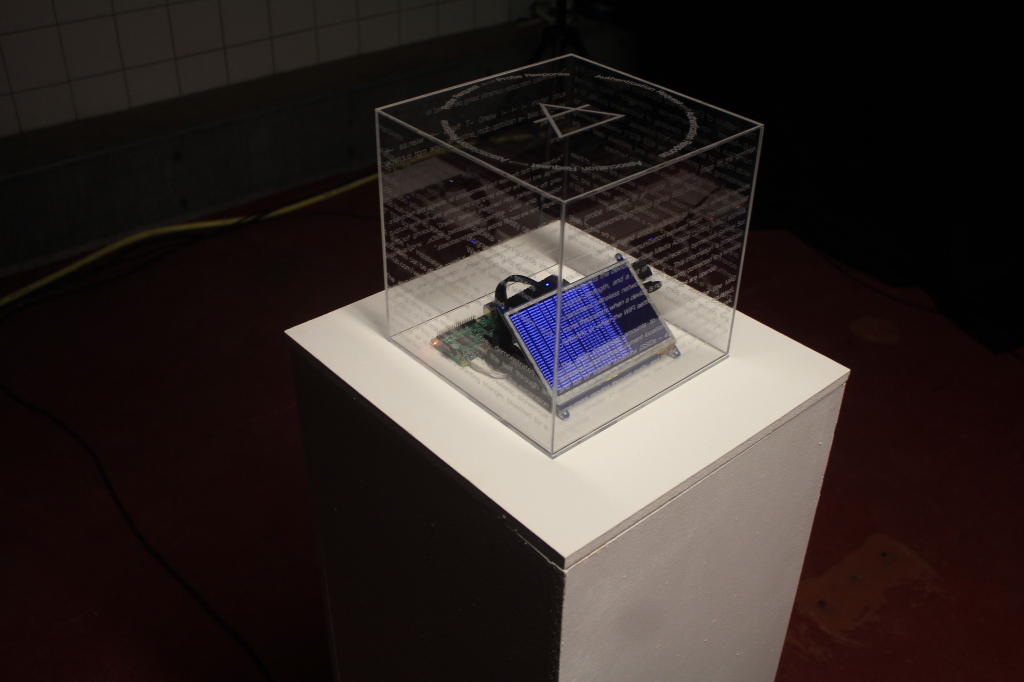
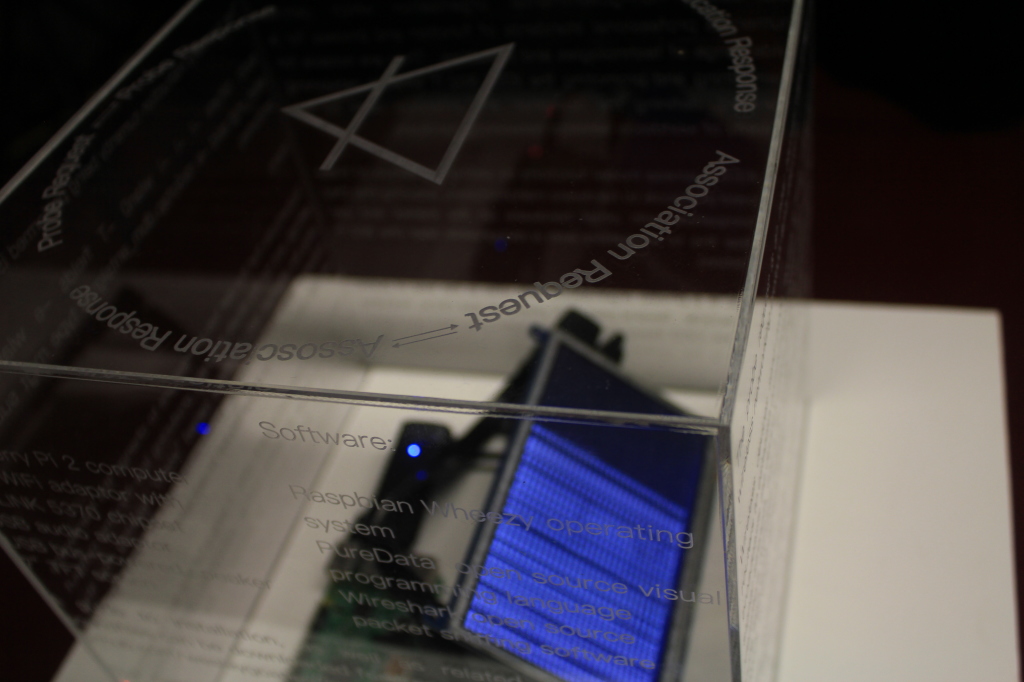
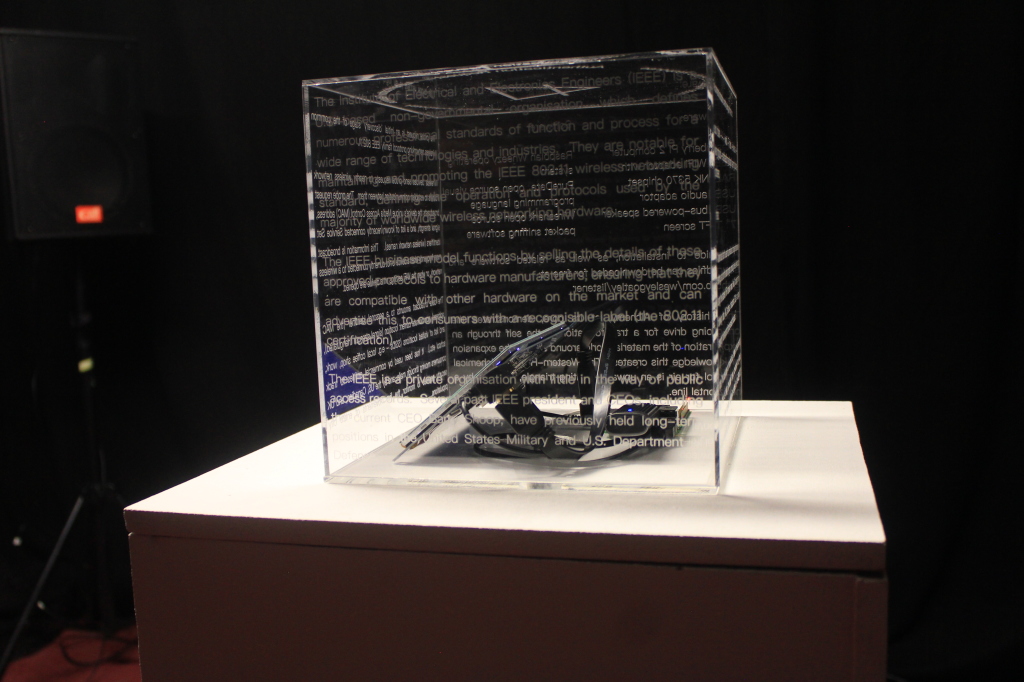
The Listener takes the form of a transparent case, laser-etched with text on all sides, with its exposed components and processes displayed. Inside, the screen shows the results of the live probe request scan being performed at that moment, allowing the form and structure of this data to be read by the owners of the devices which are generating it. The text inscribed onto the case details information such as the hardware and software used in The Listener itself, a translation of the code being run, a break down of the probe request process, and the nature of the Institute of Electrical and Electronics Engineers (IEEE), the standards body that determines function of the probe request.
The Listener is surrounded by four speakers, and sonifies detected MAC addresses by mapping each element of the MAC address to a specific vocal sample. This produces vocal ‘chants’ unique to each wireless device, that call out into the room whenever a probe request is detected. The signal strength of the device to The Listener determines the volume of the chant, so that it increases as the device approaches it; and from inside The Listener itself, the names of any broadcast SSIDs are then ‘whispered’ through a text-to-speech algorithm and internal speaker.
By employing these multiuple forms of reading the probe request process, The Listener pulls its layers and context apart for examination, experimenting with how we can read and understand the nested technological processes that we rely upon, and how we can critique their implications for privacy and control.